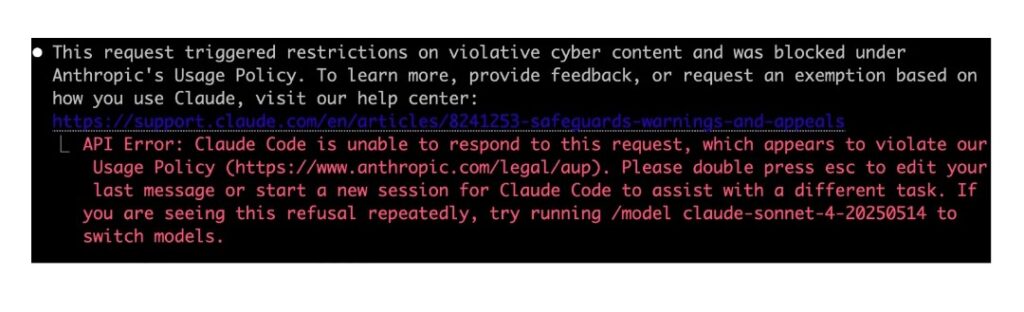
Many security researchers on Claude Code are now complaining about an annoying error message. The affected people said the exploit development and vulnerability analysis tool is misbehaving. This complaint comes because Claude Code blocks tasks that would normally work perfectly. The Claude Code error message reads: “This request triggered restrictions on violative cyber content and was blocked under Anthropic’s usage.”
Claude Code Researchers Complain About a ‘Violative Cyber Content’ Error Message
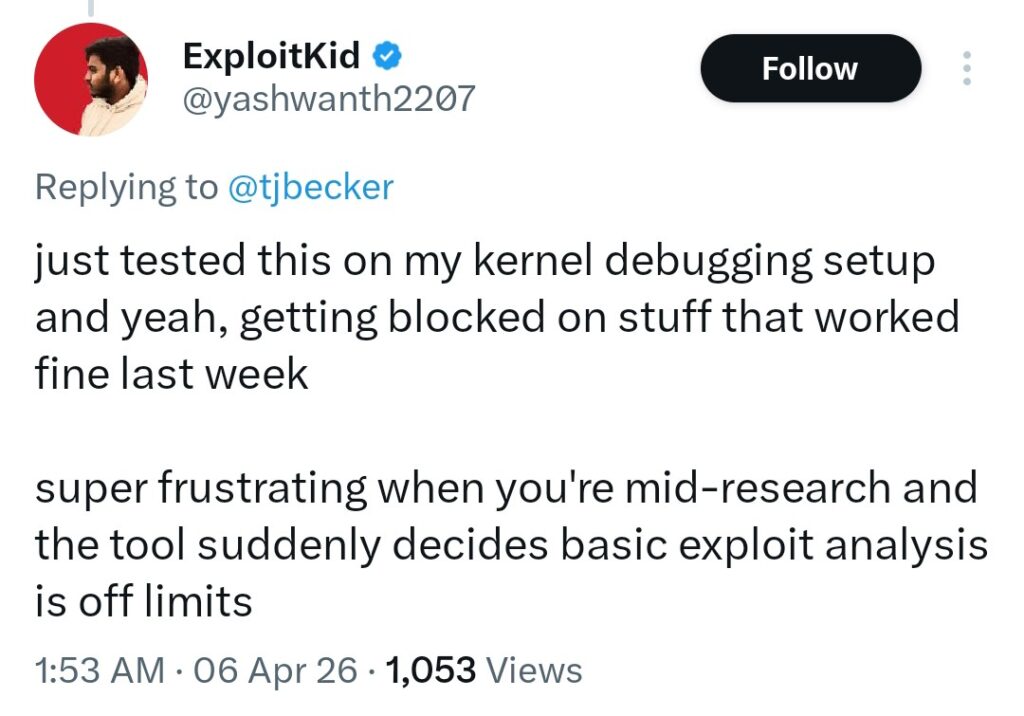
A Seattle-based security researcher, Tim Becker, shed more light on the ‘Violative Cyber Content’ issue on Claude Code. He said he tried resuming some of his exploit-dev sessions but ended up getting blocked. He further added that several other researchers are experiencing the same issue.
Another user said that after testing on his kernel debugging setup, tasks that worked fine last week got blocked. What’s even more annoying is that this issue affects almost every prompt, not just the risky ones. It’s simple; imagine having a prior context in the prompt that Claude considers “violative.” Because of this, the system ends up blocking every other follow-up message. This causes the affected researcher to restart the entire session from the beginning.
Anthropic Acknowledges the Issue
The good news is that Anthropic has already acknowledged the issue affecting Claude Code researchers. In a safeguard report, the team says it’s rolling out new cyber protections for Claude Opus 4.6. This update is designed to automatically detect and block prompts that violate cybersecurity usage under Anthropic usage.
Furthermore, Anthropic provides researchers with the Cyber Use Case Form. This offering is essential if you have legitimate work, which may be impacted by the update. It allows you to bypass the cyber content filters and continue with your sessions without disruptions. The only issue is that the approval process and timeline are unclear.
Tim Becker further analyzed the situation, emphasizing that the Claude Code ‘Violative Cyber Content’ block will only affect genuine people. He mentioned that attackers will never waste a zero-day exploit querying Anthropic’s public API to generate it.
So, what’s the way forward for legitimate researchers? The only thing you can do now to avoid getting blocked mid-project is to submit Anthropic’s exemption form. But you may have to wait a while to have your form approved.

Add Comment